Honeypots, but better.
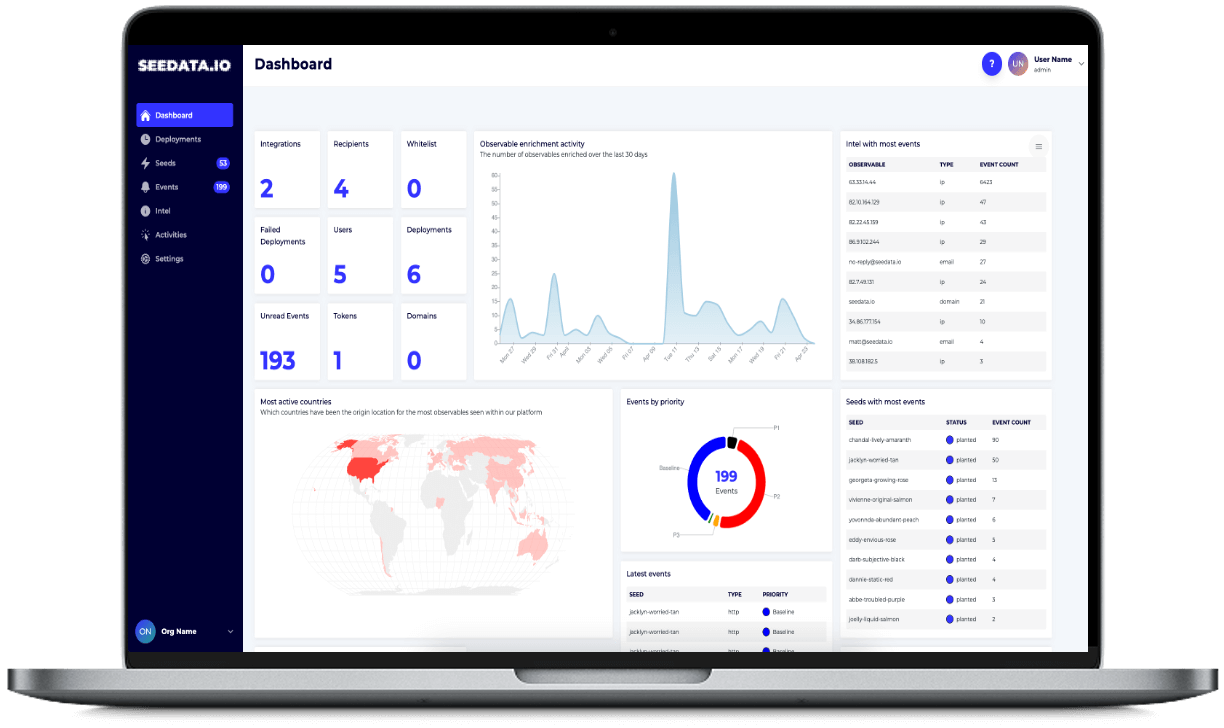
Seedata.io’s automated deception platform plants, maintains and monitors “traps” throughout your estate, catching attackers before damage is done
Seeding Data and Honeypots can be a real asset when detecting or responding to data incidents.
I was pleasantly surprised on how straightforward it was to implement Seedata.io’s take on the technology. Well worth spending the time to investigate!
SeeData helps you reduce Mean Time To Detection (MTTD) and improve your overall signal to noise ratio.
With high quality signals, they enrich their alerts with threat intelligence to provide more context around the alert, the actor, and the urgency of your next steps.
Seedata enables organisations to detect threats in their environment with high value telemetry.
This enables defenders to respond faster with far fewer false positives that would be generated with just traditional detective controls.







Do these problems sound familiar?
Rising Cybersecurity Costs
Businesses are spending more on cybersecurity tools, but threats continue to evolve, making many solutions feel like a never-ending investment treadmill.
Lack of Incident Visibility
When a breach occurs, organisations often struggle to understand its scale, origin, or timeline, wasting time and resources.
Detection Gaps in Traditional Security Tools
Traditional tools like firewalls, EDR, and SIEM systems focus on prevention or reaction, often missing sophisticated or emerging attack vectors.
Still suffering from Data Loss and Insider Threats
Organisations face risks not just from external attackers but from insiders—employees, contractors, or partners who may misuse their access intentionally or accidentally. Even with advanced defences, attackers often find ways to exfiltrate sensitive data unnoticed, often through phishing, malware, or supply chain attacks.
High Operational Overheads
You know you need to introduce new tools, but you also know your team is already stretched; implementation projects will require prioritisation, you can’t commit more time to running another platform, let alone completing the training needed.
High False Positive rates
The more you look, the more you find. But in many cases, you’re finding false positives. and you can only be sure they are false positives after traiging everything, which takes time and leads to SOC team burnout.
Deception, without the hassle
Seedata.io helps you detect threats early with zero SOC burnout. Our automated deception technology plants, changes, and maintains decoy assets across your cloud infrastructure—without requiring your team to become deception experts.
Infrastructure-as-Code Deployments
Easily deploy decoys across your entire environment using infrastructure-as-code, ensuring fast and consistent setups without hassle.
Automated Tailored Proposals
Our platform automatically generates customized recommendations on where to place decoys, how many are needed, and which assets to protect, ensuring the best coverage with minimal effort.
Alert Integrations
Receive alerts directly through our platform or integrate them into your existing security tools like SIEM, SOAR, or SOC, ensuring smooth and timely response within your current workflow.
Take a more detailed look at different scenarios where seedata.io provides value
Honeypots* & Deception: The Key to Smarter Detection
* We call them seeds
Seedata enables security teams to deploy cloud-native honeypots on autopilot, delivering high-fidelity alerts that detect intruders early
Increase Detection Coverage
Deploying our honeypots ensures broader detection across your environment, filling in the gaps where traditional security tools may miss threats.
Whether it’s cloud or on-premise, our decoys help secure every part of your network
Increase Detection Rates
Deception technology is designed to identify threats that evade traditional defenses. Using dynamic, realistic decoys, we detect intruders immediately, without relying on signatures or behavioural patterns.
This ensures that even new and sophisticated threats are caught early, improving your detection rates.
Increase Detection Fidelity
Unlike traditional security systems that rely on pattern-based alerts, our deception technology only triggers alerts when decoys are directly engaged.
This drastically reduces false positives and delivers higher-fidelity alerts that let your team focus on real, actionable threats.